In 1982, when SMTP was first specified, it did not contain any mechanism for providing security at the transport level to secure communications between the mail transfer agents. However, in 1999, the STARTTLS command was added to SMTP that in turn supported the encryption of emails in between the servers, providing the ability to convert a non-secure connection into a secure one that is encrypted using TLS protocol.
However, encryption is optional in SMTP which implies that emails can be sent even in plaintext. Mail Transfer Agent-Strict Transport Security (MTA-STS) is a relatively new standard that enables mail service providers the ability to enforce Transport Layer Security (TLS) to secure SMTP connections, and to specify whether the sending SMTP servers should refuse to deliver emails to MX hosts that that does not offer TLS with a reliable server certificate. It has been proven to successfully mitigate TLS downgrade attacks and Man-In-The-Middle (MITM) attacks. SMTP TLS Reporting (TLS-RPT) is a standard that enables the reporting of issues in TLS connectivity that is experienced by applications that send emails and detect misconfigurations. It enables the reporting of email delivery issues that take place when an email isn’t encrypted with TLS. In September 2018 the standard was first documented in RFC 8460.
Key Takeaways
- STARTTLS provides a way to encrypt emails between servers, but its implementation is optional, leaving potential vulnerabilities.
- MTA-STS enforces the use of TLS for email transport to protect against downgrade and Man-In-The-Middle attacks.
- Encryption in transit significantly enhances the information security of email communications by safeguarding against cryptographic attacks.
- TLS-RPT allows domain owners to receive diagnostic reports on email delivery issues, improving visibility and proactive troubleshooting.
- Using services like PowerDMARC simplifies the implementation of MTA-STS and TLS-RPT, reducing complexities in adopting these security standards.
Why Do Your Emails Require Encryption in Transit?
The primary goal is to improve transport-level security during SMTP communication and ensuring the privacy of email traffic. Moreover, encryption of inbound and outbound messages enhances information security, using cryptography to safeguard electronic information. Furthermore, cryptographic attacks such as Man-In-The-Middle (MITM) and TLS Downgrade have been gaining popularity in recent times and have become a common practice among cybercriminals, which can be evaded by enforcing TLS encryption and extending support to secure protocols.
Simplify Security with PowerDMARC!
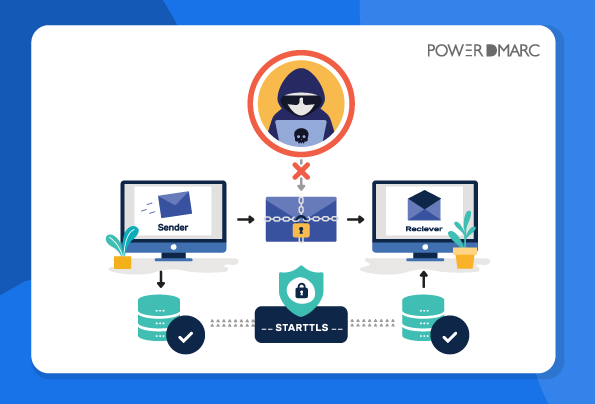
How Is a MITM Attack Launched?
Since encryption had to be retrofitted into SMTP protocol, the upgrade for encrypted delivery has to rely on a STARTTLS command that is sent in cleartext. A MITM attacker can easily exploit this feature by performing a downgrade attack on the SMTP connection by tampering with the upgrade command, forcing the client to fall back to sending the email in plaintext.
After intercepting the communication a MITM attacker can easily steal the decrypted information and access the content of the email. This is because SMTP being the industry standard for mail transfer uses opportunistic encryption, which implies that encryption is optional and emails can still be delivered in cleartext.
How Is a TLS Downgrade Attack Launched?
Since encryption had to be retrofitted into SMTP protocol, the upgrade for encrypted delivery has to rely on a STARTTLS command that is sent in cleartext. A MITM attacker can exploit this feature by performing a downgrade attack on the SMTP connection by tampering with the upgrade command. The attacker can simply replace the STARTTLS with a string that the client fails to identify. Therefore, the client readily falls back to sending the email in plaintext.
In short, a downgrade attack is often launched as a part of a MITM attack, so as to create a pathway for enabling an attack that would not be possible in case of a connection that is encrypted over the latest version of TLS protocol, by replacing or deleting the STARTTLS command and rolling back the communication to cleartext.
Apart from enhancing information security and mitigating pervasive monitoring attacks, encrypting messages in transit also solves multiple SMTP security problems.
Achieving Enforced TLS Encryption of Emails with MTA-STS
If you fail to transport your emails over a secure connection, your data could be compromised or even modified and tampered with by a cyber attacker. Here is where MTA-STS steps in and fixes this issue, enabling safe transit for your emails as well as successfully mitigating cryptographic attacks and enhancing information security by enforcing TLS encryption. Simply put, MTA-STS enforces the emails to be transferred over a TLS encrypted pathway, and in case an encrypted connection cannot be established the email is not delivered at all, instead of being delivered in cleartext. Furthermore, MTAs store MTA-STS policy files, making it more difficult for attackers to launch a DNS spoofing attack.
MTA-STS offers protection against :
- Downgrade attacks
- Man-In-The-Middle (MITM) attacks
- It solves multiple SMTP security problems, including expired TLS certificates and lack of support for secure protocols.
Major mail service providers such as Microsoft, Oath, and Google support MTA-STS. Google being the largest industry player, attains centre-stage while adopting any protocol, and the adoption of MTA-STS by google indicates the extension of support towards secure protocols and highlights the importance of email encryption in transit.
Troubleshooting Issues in Email Delivery with TLS-RPT
SMTP TLS Reporting provides domain owners with diagnostic reports (in JSON file format) with elaborate details on emails that have been sent to your domain and are facing delivery issues, or couldn’t be delivered due to a downgrade attack or other issues, so that you can fix the problem proactively. As soon as you enable TLS-RPT, acquiescent Mail Transfer Agents will begin sending diagnostic reports regarding email delivery issues between communicating servers to the designated email domain. The reports are typically sent once a day, covering and conveying the MTA-STS policies observed by senders, traffic statistics as well as information on failure or issues in email delivery.
The need for deploying TLS-RPT :
- In case an email fails to be sent to your recipient due to any issue in delivery, you will get notified.
- TLS-RPT provides enhanced visibility on all your email channels so that you gain better insight on all that is going on in your domain, including messages that are failing to be delivered.
- TLS-RPT provides in-depth diagnostic reports that enable you to identify and get to the root of the email delivery issue and fix it without any delay.
Adopting MTA-STS and TLS-RPT Made Easy and Speedy by PowerDMARC
MTA-STS requires an HTTPS-enabled web server with a valid certificate, DNS records, and constant maintenance. PowerDMARC makes your life a whole lot easier by handling all of that for you, completely in the background- from generating certificates and MTA-STS policy file to policy enforcement, we help you evade the tremendous complexities involved in adopting the protocol. Once we help you set it up with just a few clicks, you never even have to think about it again.
With the help of PowerDMARC’s Email Authentication Services, you can deploy Hosted MTA-STS at your organization without the hassle and at a very speedy pace, with the help of which you can enforce emails to be sent to your domain over a TLS encrypted connection, thereby making your connection secure and keeping MITM attacks at bay.
PowerDMARC makes your life easier by making the process of implementation of SMTP TLS Reporting (TLS-RPT) easy and speedy, at your fingertips! As soon as you sign up with PowerDMARC and enable SMTP TLS Reporting for your domain, we take the pain of converting the complicated JSON files containing your reports of email delivery issues, into simple, readable documents (per result and per sending source), that you can go through and understand with ease! PowerDMARC’s platform automatically detects and subsequently conveys the issues you are facing in email delivery, so that you can promptly address and resolve them in no time!
Sign up to get your free DMARC today!
- Microsoft Sender Requirements Enforced— How to Avoid 550 5.7.15 Rejections - April 30, 2025
- How to Prevent Spyware? - April 25, 2025
- How to Set Up SPF, DKIM, and DMARC for Customer.io - April 22, 2025