Eavesdropping and impersonation have become too common and frequent in today’s digital landscape. Threat actors deploy MITM attack techniques to access and steal sensitive details for cybercrimes. The usual targets are users of financial platforms, SaaS companies, e-commerce platforms, and other websites that require logging and contain financial details.
This blog will deeply discuss what a man-in-the-middle attack and ways to prevent it is.
Key Takeaways
- Man-in-the-middle attacks allow cybercriminals to intercept and manipulate communications between two parties without their knowledge.
- Common techniques used in these attacks include IP spoofing, DNS spoofing, and ARP spoofing, which exploit vulnerabilities in network protocols.
- Signs of a potential MITM attack include frequent disconnections and the presence of strange or misspelled URLs in the address bar.
- Practicing good internet hygiene, such as avoiding unsecured Wi-Fi networks and using a VPN, can help prevent MITM attacks.
- Email authentication protocols like MTA-STS are essential for safeguarding email communications from interception during transmission.
What is a Man in the Middle Attack?
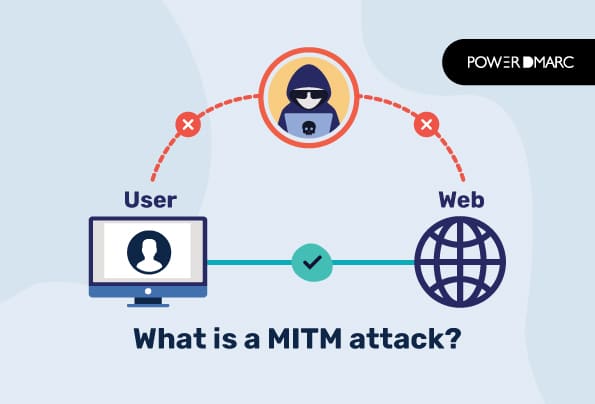
A man-in-the-middle attack or MITM attack is an eavesdropping attack in which a cyber actor obstructs communication and data transfer between the sender and receiver’s servers. They act as the third party between the communication string; thus, the name “man in the middle” is associated with this cyber activity. This way, threat actors behave as legitimate parties for both ends.
Man-in-the-middle attacks are attempted to intercept, steal, or modify data, disrupt communication, and send malicious links to either party.
Simplify Security with PowerDMARC!
Phases of a Man in the Middle Attack
There are two phases of a standard MITM attack; interception and decryption. Let’s know about them in detail.
Interception
In the interception phase of a man-in-the-middle attack, threat actors try accessing a vulnerable system and sabotage communication or data exchanged between parties with the help of malicious resources like software and tools. They behave as proxies between victims (website owners) and users (clients, prospects, etc.) to steal data and credentials or inject malware.
As malicious actors are positioned in the middle, they obtain sensitive details from senders that they can modify or corrupt before passing them on to the other end. Unsecured wifi is a common gateway for interception alongside other techniques discussed below.
- IP Spoofing
In IP spoofing, threat actors send malicious IP packets using fake IP addresses for masquerading. It’s generally used to attempt DDoS attacks or mask an attacker’s real identity. IP spoofing makes phishing more impactful and challenging to control, as fake emails appear to come from a genuine source.
IP address spoofing prevents authorities from finding out who they are, so they can’t be tracked. It averts victims’ devices from delivering notifications about attacks so that they can complete the process smoothly.
- DNS Spoofing
DNS spoofing is a cybercrime technique where hackers hijack a web browser’s request for a particular website and redirect the user to another website. Generally, the other website is fake or imitates the original one so that they can steal sensitive user details.
DNS spoofing is attempted by altering DNS servers’ IP addresses to initiate phishing attacks or injecting malware.
- ARP Spoofing
In ARP spoofing, threat actors send fraudulent ARP or Address Resolution Protocol Messages to fool other devices into perceiving they’re connected and communicating with someone else. This way, hackers steal and intercept data for malicious use.
For trying ARP spoofing, hackers either wait to access ARP requests or distribute an unauthorized message called ‘gratuitous ARP’. While the former method is less destructive and has a narrower reach, the latter is more impactful and complicated.
- Email Hijacking
Email MITM attacks are generally targeted toward banks and other financial institutions to steal customer details for supervising all transactions. Hackers also send fake emails appearing to come from a legitimate source where recipients are asked to share sensitive details. Thus, it’s important to use email authentication protocols like SPF and DMARC to prevent email hijacking attacks.
SPF ensures only authorized IP addresses can send emails using your domain, while DMARC specifies how to treat emails that fail SPF and DKIM checks ( another email authentication protocol).
Decryption
The decryption phase is the next thing to know while understanding what a MITM attack is.
After encryption, hackers decrypt the unethically obtained data in a successful MITM attack to either sell it in the black market or use it for attempting malicious activities. The stolen data is used for online transactions, forgery, masquerading, etc. The following are two common decryption methods.
- HTTPS Spoofing
In HTTS spoofing, hackers deceive your web browser into considering an illegitimate website as legitimate. They basically alter the HTTPS-based address requests to redirect them to their HTTPS-equivalent endpoints.
- SSL Hijacking
SSL is short for Secure Socket Layer, an internet-based technology for securing and safeguarding sensitive data exchanged between two IP addresses. If you visit an unsecured website whose URL starts with HTTP, an SSL-secured browser will automatically redirect you to its secure version with an HTTPS URL.
IN SSL hijacking, MITM attackers manipulate victims’ computers and servers to intercept the changed route to steal sensitive data.
Signs of a Man-in-the-Middle Attack
Hackers are becoming more sophisticated as they use readily available tools bought from the black market. This makes encryption and decryption faster and easier for them. However, it isn’t that challenging to safeguard yourself against man-in-the-middle attacks if you educate yourself and your team members on reading their signs. Let’s see what these are.
Frequent Disconnections
Hackers forcefully disconnect users to intercept their usernames and passwords when they reconnect. Consider it a red flag if you are logged out or repeatedly disconnected from a particular website.
Strange or misspelled URLs in the Address Bar
Confirm URLs if they look odd or have a spelling alteration. At times, hackers attempt DNS hijacking by creating fake websites with slight spelling changes- for example, replacing O (the 15th letter of the English alphabet) with 0 (zero). So, you might not notice that you’re visiting www.amaz0n.com instead of www.amazon.com.
Unsecured URL
Don’t visit websites whose URLs start with HTTP instead of HTTPS, especially if you’ve to do more than just read any information. These aren’t secure and encrypted, which means cybercriminals can intercept data exchanged between two parties.
How to Stop MITM Attacks?
Are you thinking about how to stop man-in-the-middle attacks? Just be cautious and practice the good internet hygiene methods shared below.
Avoid unsecured and public Wi-Fi Networks
Public wi-fi networks aren’t secured. So, avoid connecting to them while traveling or making online transactions. You can use your wireless carrier’s encrypted connection or routers with WPA2 security.
Use a VPN
Adding a VPN or Virtual Private Network encrypts traffic between endpoints and the VPN server. This makes it challenging for threat actors to succeed in a MITM attack.
Always Log Out of Crucial Websites
Don’t save passwords on browsers; always log out of sensitive websites once your activity is completed. This implies strongly on financial websites like banks and payment gateways.
Set Unique and Strong Passwords
Use unique passwords for all important platforms and change them every 3-4 months. A strong password should have at least 12 characters with uppercase letters, lowercase letters, numbers, and special symbols.
Make sure they aren’t too obvious to guess- for example, your pet’s name or birthplace.
Use Multi-Factor Authentication
Multi-factor authentication is a security method that requires more than one way (apart from the password) to access an account or device. These secondary methods are fingerprint verification, face detection, OTP, etc.
Stop Email MITM Attacks with MTA-STS
Finally, the most effective method to protect your email communications against MITM attacks is Mail Transfer Agent- Strict Transport Security (MTA-STS). This email authentication technology allows you to protect your emails in transit by making transport layer encryption mandatory in SMTP.
Knowing what a MITM attack is is important, especially for technology-driven businesses. They’re quite common in today’s digital landscape, and hackers are becoming more sophisticated in culminating their efforts into results without leaving a trace behind. This makes it important for domain owners to take adequate measures and enforce encryption during transfer to prevent attackers from intercepting their email communications.
- DMARC MSP Case Study: How Pablo Herreros Simplified DNS Record Management for Clients with PowerDMARC - December 10, 2025
- SMB1001 & DMARC: What SMBs Must Know for Email Security Compliance - December 8, 2025
- Best Domain Analyzers for Email Security in 2026 - December 5, 2025