
How to Set Up Apple Branded Mail Using Apple Business Connect
BlogLearn how to set up Apple Branded Mail in Apple Business Connect. Enhance your email security with DMARC compliance and display your brand logo in inboxes.

Dealing with Broken SPF
BlogHow to deal with broken SPF? A broken SPF record can invalidate your authentication system, you need to fix it now!

Data Breach and Email Phishing in Higher Education
BlogExplore the growing risks of data breaches in higher education. Learn how universities and colleges face cybersecurity threats.

10 Best DMARCLY Alternatives to Optimize Your Email Security
BlogDiscover the best DMARCLY alternatives for DMARC management. Compare features, pricing, pros, and cons to find the perfect fit for your email security needs.
What is DMARC? Guide to DMARC Email
Blog, DMARCDMARC, is a powerful tool to prevent phishing attacks and ensure legitimate emails reach your inbox. Learn what is DMARC in simple terms and protect your brand.
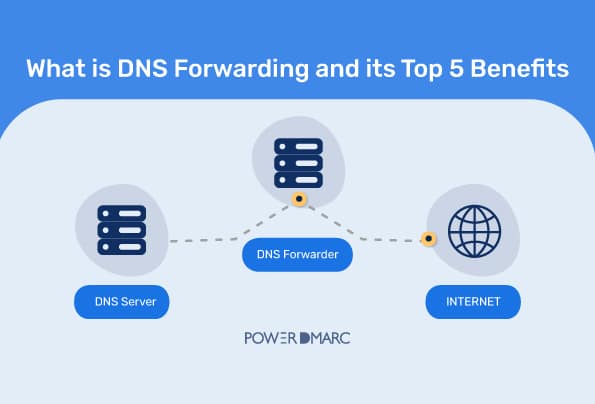
What is DNS Forwarding and Its Top 5 Benefits
BlogUnderstand DNS forwarding, its types, and best practices to enhance network performance, efficiency, and security.
