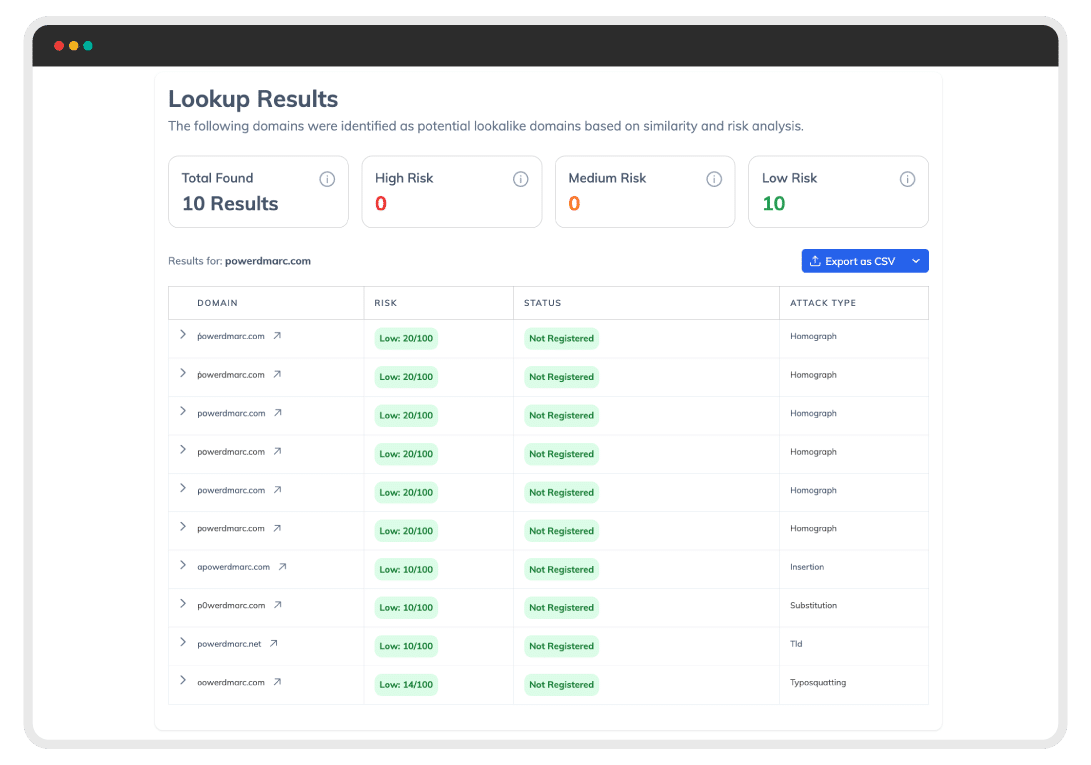
Free lookalike domain checker
A lookalike domain is a domain name that closely resembles a legitimate domain. These domains may be registered and controlled by third parties to impersonate an organization, mislead users, or carry out phishing and other malicious activities.