Phishing vs Spam
BlogPhishing and spam are both designed to trick you into taking action you wouldn't normally take, such as opening an attachment or clicking on a link.

Email Spoofing vs. Phishing: Key Differences and How to Stay Protected
BlogWhat's the difference between email spoofing vs. phishing? Learn how the attacks work, how they overlap, and proven strategies for protection.

Most Underrated Information Security Controls
BlogInformation security controls are the activities, procedures, and mechanisms that you put in place to protect yourself from cyber threats.
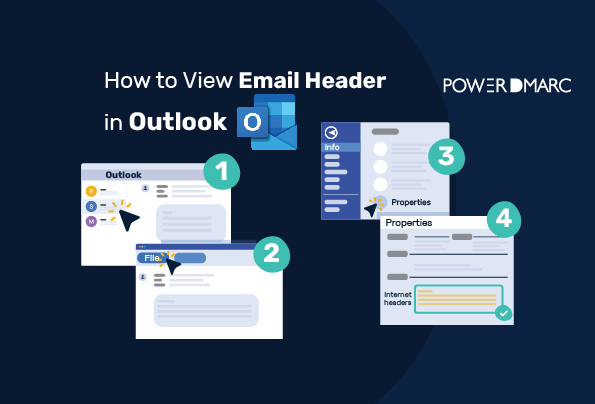
How to View Email Headers in Outlook?
BlogTo view email header in outlook, double click on the email whose email header you want to see. Select “Actions” from the menu at the top of the window.

Display Name Spoofing: Definition, Technique, Detection, and Prevention
BlogIn display name spoofing, hackers make fraudulent emails look legitimate by using different email addresses but the same display names.
How to View DNS Records for a Domain?
BlogTo view DNS records for a domain, you need to perform a lookup on your domain name system. This is an instant and easy process and here are the steps for it.
