Poland DMARC & MTA-STS Adoption Report 2026
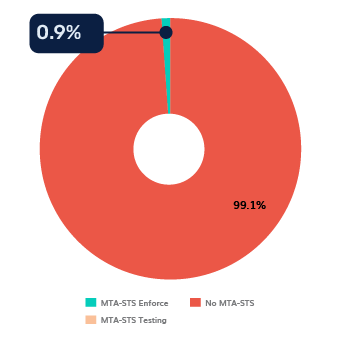
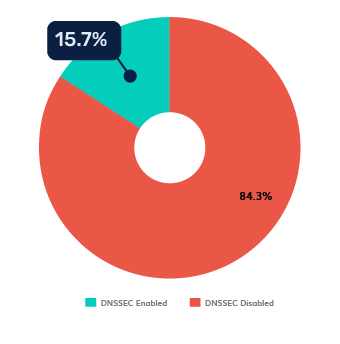
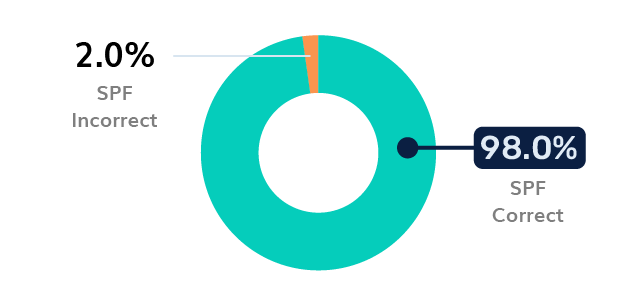
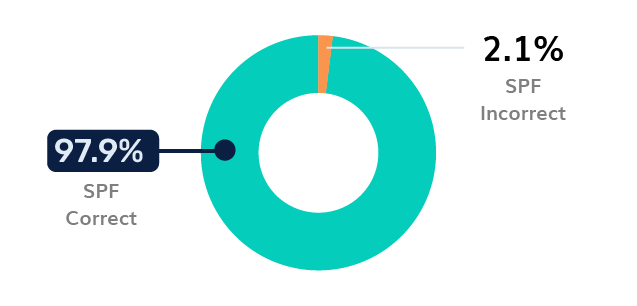
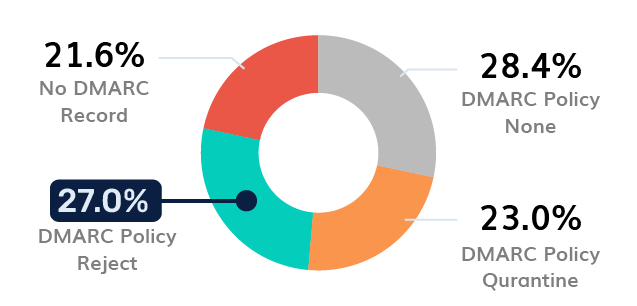
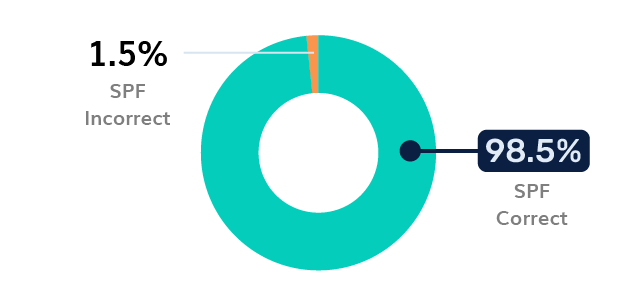
In 2026, Poland has emerged as the top regional target for cyberattacks, with state institutions facing an average of 3,188 attempts per week, a 120% increase over previous years. Despite a 98.9% SPF correctness rate, the nation remains uniquely vulnerable due to an “enforcement gap.”
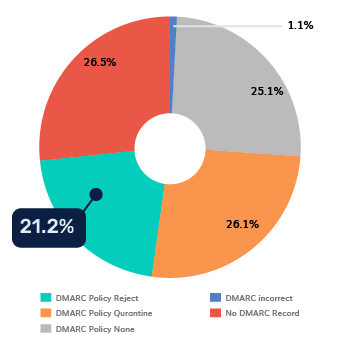
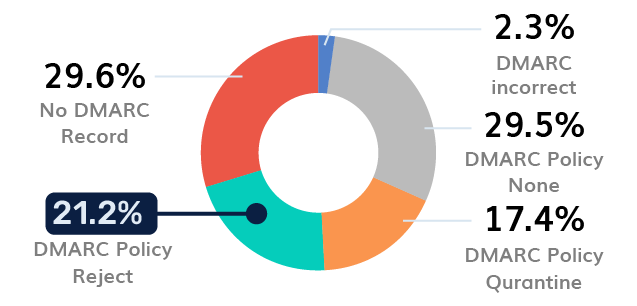
While Polish IT teams are disciplined at listing authorized senders, they are hesitant to block unauthorized ones. Only 21.2% of domains enforce a DMARC “Reject” policy, leaving nearly 80% of the digital landscape in a passive monitoring state. This vulnerability is being exploited by a new wave of AI-driven phishing, which has seen a 400% rise in success rates in 2025-2026. Attackers now use Large Language Models (LLMs) to craft perfect Polish-language lures in under five minutes, bypassing traditional “bad grammar” filters.
Report Request - Poland DMARC Adoption
"*" indicates required fields