A phishing email is like a disguised imposter in your inbox. It masquerades as a trustworthy source, aiming to deceive and manipulate you into revealing sensitive information or performing harmful actions. Email phishing has evolved over the years from simple pranks, like those experienced by early AOL users in the mid-90s involving random credit card generators, to sophisticated, highly lucrative activities for hackers across the world using advanced impersonation tactics. It’s a digital con artist that preys on human vulnerabilities and gullibility.
They can lead to devastating consequences, such as identity theft, financial loss, or unauthorized access to your accounts. According to Verizon’s 2019 Data Breach Investigation Report, approximately 32% of data breaches experienced that year involved email phishing and social engineering. Stay cautious and skeptical, for the phishing email’s sole purpose is to deceive and exploit you.
Key Takeaways
- Phishing emails manipulate recipients by masquerading as reputable sources, often using social engineering and urgency to extract sensitive information or induce harmful actions.
- Phishing has evolved into sophisticated attacks like Business Email Compromise (BEC), resulting in significant financial losses for organizations through impersonation.
- Carefully inspect sender email addresses, look for generic greetings, poor grammar/spelling, and unexpected requests for personal information or urgent actions.
- Be wary of unexpected attachments or links, even if they seem to come from known contacts, as they can lead to malware or credential theft.
- Implementing email authentication (SPF, DKIM, DMARC) is crucial for domain protection, providing visibility and control against impersonation attempts and spoofing.
What is a Phishing Email?
A phishing email is a fraudulent message designed to trick recipients into revealing sensitive information or performing actions that benefit the attacker. It’s a form of social engineering where fraudsters send emails that often look like they come from an organization or individual you trust, such as your bank, a government agency, or even someone in your own company, aiming to trick people into giving up confidential information. These emails often mimic legitimate communication from trusted sources, such as banks, online services, or well-known companies. Email phishing is becoming more common as people spend more time online.
Simplify Phishing Security with PowerDMARC!
How Do Phishing Emails Work?
Phishing emails work by employing deceptive tactics to trick recipients into divulging sensitive information or performing certain actions. These emails typically impersonate legitimate organizations or individuals to gain the trust of the recipient. Here’s an interesting breakdown of how a typical phishing email operates:
- Masquerade: Phishing emails often appear as if they are sent from reputable sources, such as banks, social media platforms, or well-known companies. The email address and content are crafted to closely resemble those of the legitimate entity, making it harder to distinguish them from genuine communication.
- Urgency or Fear: To manipulate the recipient’s emotions, phishing emails often create a sense of urgency or fear. They may claim that there is an issue with the recipient’s account, such as unauthorized activity or an imminent service suspension. By generating anxiety, the attackers aim to prompt hasty actions without careful consideration.
- Social Engineering: Phishing emails leverage social engineering techniques to exploit human psychology. They rely heavily on these techniques, taking advantage not of flaws in a system’s security infrastructure, but in the inevitability of human error. They may use various tactics like personalization, flattery, or fear of missing out (FOMO) to increase their chances of success. By preying on emotions and psychological triggers, attackers attempt to override the recipient’s rational thinking.
- Deceptive Links or Attachments: Phishing emails typically contain links or attachments that lead to malicious websites or malware-infected files. The links may appear legitimate but actually direct the recipient to a fake website that resembles the target organization’s login page. Once the victim enters their credentials, the attackers harvest them for unauthorized access.
- Data Harvesting: Phishing emails aim to collect sensitive information such as usernames, passwords, credit card details, or personal identification information. These credentials can be used for identity theft, unauthorized transactions, or gaining unauthorized access to various accounts.
- Exploitation: Once attackers obtain sensitive data, they can exploit it for various purposes. This may include unauthorized access to the victim’s accounts, financial fraud, selling the information on the black market, or launching further targeted attacks, such as spear-phishing.
How to Spot a Phishing Email?
You can easily spot a phishing email by carefully inspecting the email’s format, inconsistencies in the sender address, spelling errors, poor construction, and over-the-top claims or lures. Check the subject line and body of the email for spelling errors or other warning signs that it may be fake; grammatical errors or awkward phrasing can indicate a non-native speaker or a hastily crafted fake message. Let’s explore below:
-
Generic Greetings or Salutations
Phishing emails often use generic greetings like “Dear Sir/Madam” or “Valued Customer.” Legitimate emails usually address recipients by their names.
-
Requests for Personal Information
Legitimate organizations rarely ask for personal or financial information via email. Be cautious if an email requests sensitive data, such as Social Security numbers or login credentials.
-
Unusual Sender Email Address
Inspect the sender’s email address carefully. Phishing emails may use misspelled or suspicious domain names that mimic legitimate ones. If it doesn’t match what you’re used to seeing on official communications from that company or government agency, then it’s probably not legitimate.
-
Unexpected Attachments or Downloads
Exercise caution when receiving malicious email attachments or download links, even if they appear to come from someone you know. Malicious files can contain malware or ransomware.
Common Types of Phishing Emails
Spoofing, spear phishing, whaling, pharming, and BEC are some common types of phishing emails. While their victim profile or modus operandi may slightly differ, they are likely to cause harm to organizations and individuals.
1. Email Spoofing
Email spoofing involves forging the sender’s email address to make it appear as if the email is coming from a trusted source. Attackers may impersonate banks, government agencies, or popular online services to deceive recipients into revealing sensitive information. The purpose of an attack like this is to coax the recipient into opening the mail and possibly even clicking on a link or beginning a dialogue with the attacker. These attacks rely heavily on social engineering techniques. For example, in September 2019, Toyota lost $37 million when hackers spoofed an email address and convinced an employee with financial authority to alter account information for an electronic funds transfer.
2. Spear Phishing
Spear phishing is a targeted form of phishing where cybercriminals tailor their emails to a specific individual or organization. They gather personal information from various sources to make the email appear more legitimate and increase the chances of success.
3. Whaling Attacks
Whaling attacks target high-profile individuals, such as executives or CEOs, by impersonating trusted contacts or colleagues. These emails often aim to obtain sensitive company information or initiate fraudulent financial transactions. Vendor Email Compromise (VEC) is a related threat where attackers compromise employees at a vendor company to exploit the business relationship, sometimes impersonating executives to authorize fraudulent payments. For instance, Nikkei Inc. lost $29 million when an employee at their American office transferred money based on instructions from scammers impersonating a management executive.
4. Pharming
Pharming involves redirecting users to fake websites without their knowledge. Cybercriminals exploit vulnerabilities in DNS (Domain Name System) servers or use malicious software to modify DNS settings, leading users to phishing websites even when they enter legitimate URLs.
5. Business Email Compromise (BEC)
BEC is when an attacker gains access to a business email account and uses it to impersonate the owner, often to defraud the company, its employees, clients, or partners. According to the FBI’s 2019 Internet Crime Report, BEC scams resulted in over $1.7 billion in reported losses that year, accounting for more than half of all cybercrime losses. This is a very lucrative form of attack, which is why it remains a popular cyber threat. For example, a town in Colorado lost over $1 million after an attacker submitted a form requesting electronic payments for a local construction company, tricking an employee into updating payment information and diverting funds.
Phishing Email Examples
Check out some examples of phishing emails so you can be skeptical whenever you receive similar emails:
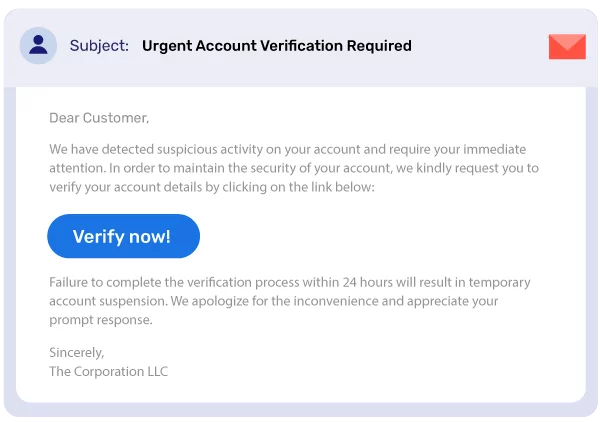
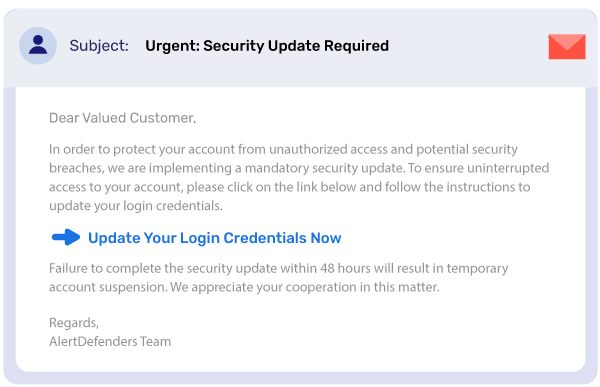
1. “Urgent Account Verification”
Phishing emails often make urgent requests, such as asking you to verify your account information or click on a link to update your security settings. These requests are designed to create a sense of urgency and make you less likely to think critically about the email.
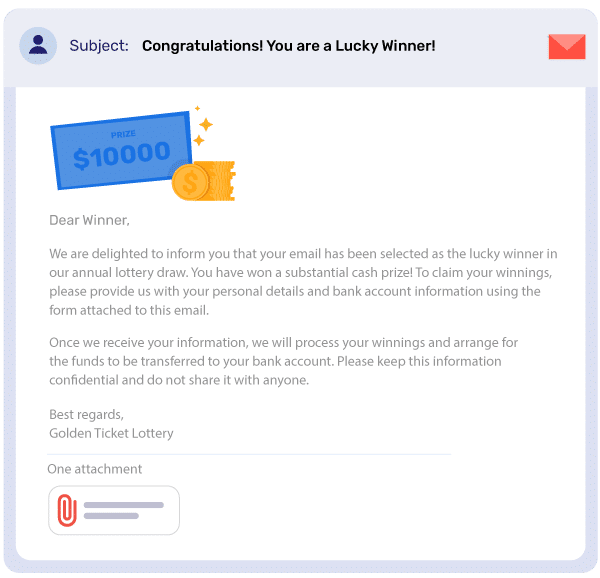
2. “Lottery Winner Notification”
This phishing email claims that you have won a lottery and asks you to provide personal information to claim your prize. The email may look like it is from a legitimate lottery company, but it is actually fake. The phisher will use your personal information to commit identity theft or other crimes.
3. “Important Security Update”
This phishing email claims that there is an important security update for your software and asks you to click on a link to download it. The email may look like it is from a legitimate software company, but it is actually fake. The link will actually take you to a website that contains malware. Once you download the malware, the phisher will be able to control your computer.
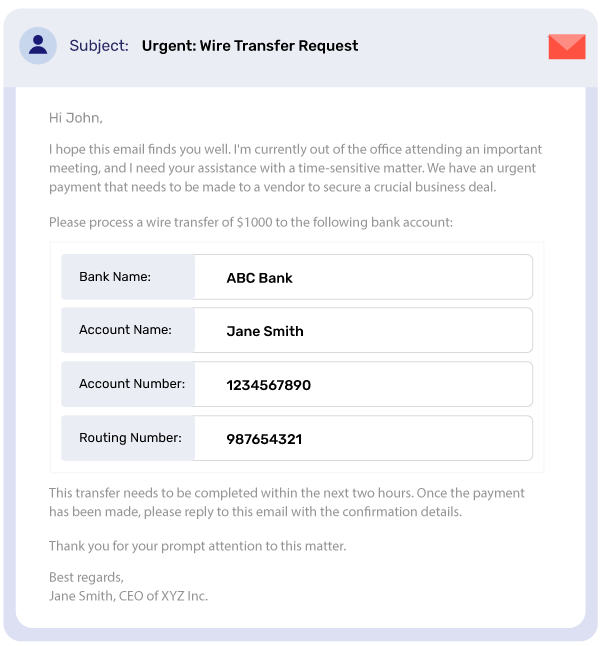
4. “Urgent Wire Transfer Request”
This phishing email claims that there is an urgent wire transfer request and asks you to provide your bank account information. The email may look like it is from a legitimate bank, but it is actually fake. The phisher will use your bank account information to steal your money.
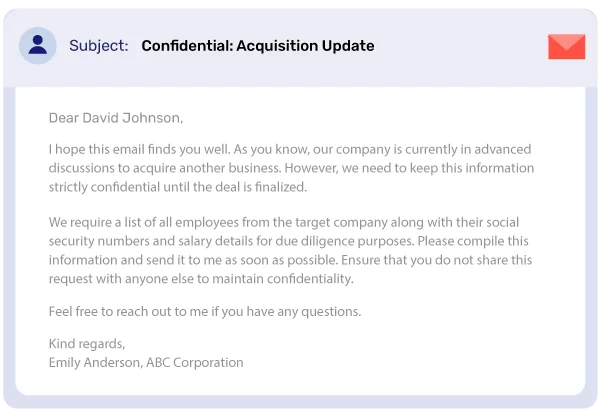
5. “Confidential Acquisition Information”
This phishing email claims that you have been selected to receive confidential acquisition information and asks you to click on a link to download it. The email may look like it is from a legitimate company, but it is actually fake. The link will actually take you to a website that contains malware. Once you download the malware, the phisher will be able to control your computer.
Protect Yourself from Phishing Emails
To protect themselves from phishing emails, individuals and organizations must stay vigilant enough to up on warning signs, avoid getting tempted by sudden lures, train themselves to detect phishing emails, and implement necessary protocols and tools for enhanced security. Global spending on security solutions reflects this need, forecasted to reach $133.7 billion in 2022 according to IDC, yet the uptake of specific email security like DMARC has been slow.
To stay safe from phishing emails:
#1 Be Skeptical
Exercise caution with unsolicited emails, especially those requesting personal information or immediate action.
#2 Verify the Sender
Check the email address and domain carefully to ensure they match the official source.
#3 Don’t Click Suspicious Links
Hover over links to reveal the actual URL destination before clicking.
#4 Avoid Sharing Sensitive Information
Legitimate organizations rarely ask for sensitive details via email.
#5 Keep Software Updated
Regularly update your operating system, antivirus software, and web browser to patch security vulnerabilities.
#6 Implement email authentication
Email authentication with SPF, DKIM, and DMARC is crucial to protecting your domain against phishing emails and helps authorize senders to minimize impersonation attempts. DMARC technology is particularly effective in preventing targeted BEC attacks by working with SPF and DKIM to determine actions against unauthenticated emails. It provides increased visibility through reports offering detailed insight into email activity and enhances security by enabling tracking and quick response to spoofing threats.
Report Phishing Emails
If you suspect that you have received a phishing email, you should:
- Notify Your Email Provider: Most email services have mechanisms in place to report phishing emails. Look for options to mark emails as spam or report phishing.
- Report to Anti-Phishing Organizations: Organizations like the Anti-Phishing Working Group (APWG) or the Internet Crime Complaint Center (IC3) can help take action against cybercriminals.
- Inform the Impersonated Entity: If a phishing email impersonates a reputable organization, notify them so they can take appropriate measures to protect their customers.
Conclusion: Stay One Step Ahead of Phishing
Phishing emails continue to pose a significant threat to individuals and organizations alike, evolving into sophisticated attacks like BEC and VEC that cause substantial financial damage. By understanding the tactics employed by cybercriminals and adopting security measures, you can minimize the risk of falling victim to their deceptive schemes. Remember to stay vigilant, think twice before clicking or sharing sensitive information, and report any suspicious emails to protect yourself and others. Implementing robust email authentication like DMARC is key to bolstering defenses against domain impersonation.
Contact us today for advanced protection against phishing and many such email-based threats and let us formulate a strategy for you that will show real results!