
Top 7 Best Email Verification Tools for Secure Delivery
BlogDiscover the best email verification tools to clean your list, reduce bounces, and improve deliverability for safer, more effective email campaigns.
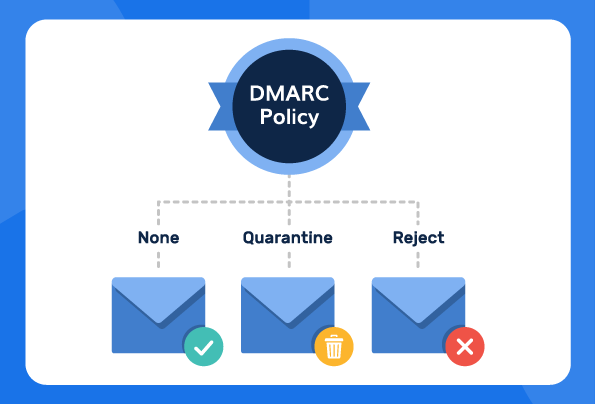
What is a DMARC Policy? None, Quarantine, and Reject
Blog, DMARCLearn what a DMARC policy is, explore all three policy options, and discover how to enforce DMARC to stop phishing and domain spoofing.

How to Set Up SPF, DKIM, and DMARC for One.com
Blog, ESP AlignmentLearn how to correctly configure SPF, DKIM, and DMARC on One.com to protect your domain from spoofing and improve email deliverability.

Email Health Check: What It Means and How to Run It
BlogLearn what email health is, why it matters, and how to improve it for better deliverability. Check your email health today.
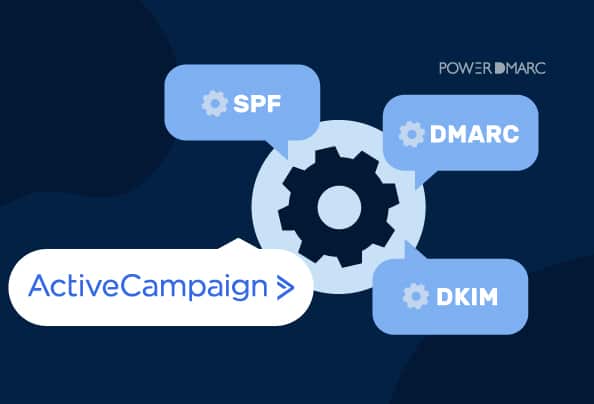
ActiveCampaign DKIM, DMARC, and SPF Setup Guide
Blog, ESP AlignmentLearn how to correctly set up DKIM, DMARC, and SPF for ActiveCampaign to improve deliverability and protect your domain from spoofing.

Constant Contact DKIM and DMARC Setup Guide
Blog, ESP AlignmentLearn how to set up DKIM and DMARC for Constant Contact to achieve full authentication, improve deliverability, and protect your domain.
