DNS vulnerabilities are often overlooked in cybersecurity strategies, despite DNS being a “phonebook” of the internet. DNS enables seamless interaction between users and websites by converting human-readable domain names into machine-readable IP addresses. Unfortunately, these same vulnerabilities make it a prime target for cyberattacks, resulting in data breaches, service outages, and significant reputational harm.
The IDC 2022 Global DNS Threat Report states that over 88% of organizations from all over the world have been victims of DNS attacks. On average, companies face seven such attacks annually. Each incident costs approximately $942,0007.
Key Takeaways
- DNS vulnerabilities can lead to severe consequences such as data breaches, service outages, and reputational damage.
- Common DNS issues include open resolvers, lack of DNSSEC, poor server configurations, and insufficient monitoring.
- Emerging threats like AI-driven DNS attacks and zero-day exploits present new challenges for network security.
- Implementing DNSSEC and real-time monitoring can significantly reduce DNS-related vulnerabilities.
- Regular vulnerability scans and infrastructure audits are essential for maintaining a secure DNS environment.
What Are DNS Vulnerabilities?
DNS vulnerabilities are weaknesses in the Domain Name System that can be exploited by attackers to compromise network security.
A DNS attack example is DNS tunneling. This practice allows attackers to compromise and endanger network connectivity. As a result, they can gain remote access to a targeted, vulnerable server and exploit it.
DNS vulnerabilities can also enable cybercriminals to target and take down crucial servers, steal sensitive data, and direct users to fraudulent, dangerous sites.
Simplify DNS Vulnerabilities with PowerDMARC!
5 Critical DNS Vulnerabilities Putting Your Network at Risk
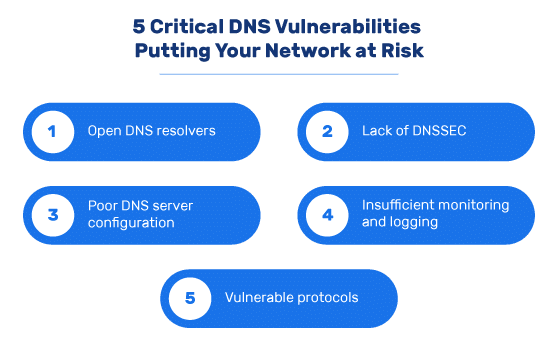
Some vulnerabilities might be so serious that they may put your network at risk. Here is a DNS Vulnerabilities list that highlights some of the more pervasive types of DNS attacks
- Open DNS resolvers
- Lack of DNSSEC
- Poor DNS server configuration
- Insufficient monitoring and logging
- Vulnerable protocols.
1. Open DNS Resolvers
Running an open browser implies serious security risks. An open DNS resolver is a resolver that is exposed to the Internet and allows queries from all IP addresses. In other words, it accepts and responds to queries from any source.
Attackers can abuse an open resolver to initiate a Denial of Service (DoS) attack, putting the entire infrastructure at risk. The DNS resolver inadvertently becomes an actor in DNS amplification, a distributed denial-of-service (DDoS) attack wherein attackers use DNS resolvers to overwhelm a victim with traffic.
Some mitigation steps include restricting access to DNS resolvers, implementing rate-limiting (RRL), and allowing queries only from trusted sources.
A useful tool to help secure DNS resolvers and prevent abuse is the Cisco Umbrella. This is a cloud-based network security platform that offers users a first layer of defense against digital cyber threats.
2. Lack of DNSSEC
DNSSEC provides a secure domain name system through the addition of cryptographic signatures to existing DNS records. A lack of DNSSEC implies that cybercriminals can manipulate your DNS records and thereby succeed in redirecting internet traffic to unauthorized, malicious websites. This can lead to identity theft, significant financial loss, or other forms of privacy and security losses.
To avoid the above, you can enable DNSSEC on your DNS servers, perform regular DNSSEC validation, and conduct periodic audits of DNSSEC implementation.
Also, try using a DNSSEC checker for validation to ensure proper implementation.
3. Poor DNS Server Configuration
DNS server misconfigurations may include open zone transfers and weak access controls. Regardless of the type of misconfiguration, you may face serious attacks, such as flood attacks and remote code execution. Flood attacks (aka Denial of Service (DoS) attacks) refer to the type of threats where attackers send an excessively high volume of traffic to a system, interrupting it from examining permitted network traffic. In a remote code execution, an attacker manages to access and make changes to the victim’s device remotely. Both types may lead to information leaks and data breaches.
Mitigation steps for DNS server misconfiguration include disabling unauthorized zone transfers, enforcing strict permissions on DNS servers, and regularly reviewing and updating DNS server configurations. You can use tools like Qualys, a DNS vulnerability scanner to identify misconfigurations.
4. Insufficient Monitoring and Logging
Not monitoring your DNS traffic consistently can leave your network vulnerable to DNS hijacking and DNS tunneling attacks. Therefore, it is important to implement real-time DNS traffic monitoring, enable detailed logging of DNS queries and responses, and regularly analyze logs for suspicious patterns.
To help yourself in the process, you can make use of intrusion detection systems that can help monitor DNS traffic for anomalies.
5. Vulnerable Protocols
The use of unencrypted UDP for DNS queries leaves them open to spoofing and eavesdropping attacks. Therefore, you should implement DNS over HTTPS (DoH) or DNS over TLS (DoT).
Other helpful steps include using DNSSEC in conjunction with encrypted DNS protocols and enforcing TLS/HTTPS for all DNS communications. You can try using Cloudflare DNS which provides a fast and private way to browse the Internet.
Simplify DMARC with PowerDMARC!
Emerging DNS Security Vulnerabilities
In addition to existing attacks, new forms of DNS attacks emerge. For example, AI-driven DNS attacks and Zero-day DNS exploits are likely to further endanger users from all around the world.
While people have already come up with effective strategies to fight and mitigate existing DNS attacks, we need to work hard to devise strategies that would enable us to fight emerging DNS attacks. This requires us to be consistently informed about the latest developments and be agile enough to come up with quick, effective responses to emerging threats.
1. AI-Driven DNS Attacks
Artificial intelligence is being used to automate and scale DNS attacks, making them more sophisticated and harder to detect. You can choose to respond to AI-driven attacks in the ‘language’ of AI, by utilizing AI-based threat detection tools yourself. You should also regularly update your security measures to counter evolving AI-driven attacks.
2. Zero-Day DNS Exploits
Unpatched vulnerabilities in DNS software can be exploited before fixes are available. This may pose a significant risk to network security. Ensure to monitor CVE databases for new DNS vulnerabilities, conduct regular vulnerability scans of DNS infrastructure, and implement virtual patching when immediate updates are not possible.
Why DNS Security Matters: Understanding the Risks
DNS serves as the backbone of internet communication. Vulnerabilities in DNS can lead to severe consequences, which include:
Data theft through DNS tunneling and spoofing
DNS tunneling is a type of DNS attack technique that involves embedding the details of other protocols in DNS queries and responses. The data payloads associated with DNS tunneling may latch onto a target DNS server, thereby enabling cybercriminals to seamlessly control remote servers.
During DNS tunneling, the attackers make use of the external network connectivity of the exploited system. Attackers also need to gain control over a server that may function as the authoritative server. This access will enable them to conduct server-side tunneling and facilitate data theft.
Service outages from DDoS attacks leveraging DNS amplification
DNS amplification is a type of DDoS attack that makes use of DNS resolvers with the goal of overwhelming the victim with excessive traffic. The overwhelming volume of the unauthorized traffic can strain and overwhelm network resources. This might result in service outages lasting minutes, hours, or even days. Organizations focused on achieving zero downtime design their infrastructure so alternative systems automatically take over when primary components fail.
Reputational damage resulting from DNS hijacking and cache poisoning
Whereas DNS poisoning refers to the corruption of the domain name system wherein users are directed to dangerous websites, domain hijacking leads to the unauthorized transfer of domain ownership, which comes with serious financial and reputational damages.
Cache poisoning may also lead to reputational damages since it can simultaneously affect multiple users and put their sensitive information at risk.
Preventing DNS Vulnerabilities

To protect your network from DNS-based attacks, it is important to recognize the critical role of DNS infrastructure in maintaining internet functionality and security.
Exploited DNS vulnerabilities can result in severe consequences such as data breaches, malware infections, service disruptions, and financial losses. Cyber attackers often target DNS servers to redirect users to malicious websites, intercept sensitive data, or render services unavailable.
- Enable DNSSEC to cryptographically validate DNS responses.
- Implement a robust patch management process for DNS software.
- Harden DNS server configurations by restricting access.
- Monitor DNS traffic in real-time to detect anomalies and potential attacks.
- Conduct regular vulnerability scans of your DNS infrastructure.
Consider using PowerDMARC’s DNS Timeline & Security Score History to improve your domain’s security posture over time. Our DNS Timeline feature is multi-faceted and offers well-rounded benefits for comprehensive DNS record monitoring. Here are some of the many features that our tool offers:
Thorough DNS Change Tracking
PowerDMARC’s DNS Timeline feature offers a detailed overview of your DNS records while also accounting for any updates and changes that take place. It monitors changes in:
- DMARC policies.
- SPF rules.
- DKIM selectors.
- BIMI logos.
- MTA-STS, MX, A, NS, TLS-RPT, TXT, and CNAME records.
The tool also captures each change in a visually appealing, easy-to-understand format. It offers:
- Corresponding, relevant timestamps for thorough monitoring.
- Domain security ratings that help quantify the information and make it easier to measure.
- Important validation statuses which indicate any missing elements in the configuration or the lack thereof.
Easy-to-understand descriptions of the changes
PowerDMARC’s tool describes DNS record changes in a way that is easy to follow by the users. The DNS Timeline feature displays both old and new records side by side.
Additionally, it includes a dedicated column where it lists the differences in the new record. This helps even those who are completely new to the field and are not technically equipped to read, analyze, and draw comparisons between old and new records.
Filtering option
You can filter DNS changes according to domains or subdomains, record types (e.g. DMARC or SPF), time ranges, etc.
Security Score History tab
The Security Score History tab offers an easy-to-follow, graphical representation of your domain’s security rating over time.
Final Words
In this article, we covered critical insights on what DNS vulnerabilities are, why DNS security matters, and what actions to take to prevent such vulnerabilities. The correct implementation of DNSSEC, DMARC, DKIM, and SPF can help your business improve its domain security, while also preventing a range of email security vulnerabilities.
PowerDMARC can help you with the correct implementation of DNS records for configuring email authentication protocols. With automated tools, AI-driven insights, and simplified reports it’s a one-stop solution for your domain security needs!
Don’t wait for a breach—secure your domain with PowerDMARC today! Sign up for a free trial and experiment with our tools by yourself to see the potential positive effects on your organization’s overall security standing.
- How to Send Secure Email in Outlook: Step-by-Step Guide - April 2, 2026
- SPF Compression: Reduce SPF DNS Lookups and Optimize Your SPF Record - March 25, 2026
- Verified Mark Certificate vs Common Mark Certificate: Choosing the Right One - March 10, 2026