Google Calendar Invite Responses Blocked by DMARC
Have you ever had the experience of an email invitation from a company or organization that you really want to respond to, only to realize that DMARC completely blocks it? If so, you’re not alone.
DMARC is a “domain-based policy” designed to prevent spam and phishing attacks. It’s a great tool for stopping unwanted emails, but it can also be a pain if your DMARC settings are set up incorrectly or if you’ve made some changes to your email account that are not reflected in your DNS records. The mailbox provider you use, or the way you respond to your invite also plays a huge role in blocking responses.
In this article, we’ll go over how to fix DMARC blocking Google Calendar invites and get them to reach your host, as intended!
Key Takeaways
- DMARC is effective for preventing spam and phishing, but can also block legitimate email responses if misconfigured.
- SPF and DKIM both play crucial roles in ensuring DMARC compliance and preventing authentication failures.
- Using out-of-band response buttons significantly reduces the likelihood of calendar invite responses being blocked.
- Modifying your SPF record to include Google as an authorized sender can help prevent issues with blocked invites.
- Changing your DMARC policy to p=none can relieve blocking but exposes your domain to spoofing risks.
The reason behind Google Calendar invite responses blocked by DMARC
Discrepancies in SPF authentication while using Google Workspace
Let’s suppose you’re a company with your own domain (e.g company.com) hosted on google workspace, and avidly use google applications (such as Google Calendar) to interact within and outside your organization. It’s important to note that the technology behind Google is still evolving, and there can be verification discrepancies while using some internal applications.
For example, if you have been sent a calendar invite using Google Calendar, the return-path domain will still point to a Google domain instead of company.com. This google domain, not listed on your domain’s SPF record, will return an SPF fail status. When this happens, email-receiving servers perceive the email containing the google calendar invite response as spammy or fraudulent. Your DMARC policy (set to p=reject) will then block this message and prevent your host from receiving your response altogether.
This is bad news, especially because it was a legitimate email that was blocked.
Simplify Security with PowerDMARC!
How to ensure your Google Calendar invite responses pass the DMARC check?
If you have your google calendar invite responses blocked by DMARC, you can exercise the following steps to evade this problem. Note that we have provided multiple options for you to select one that works best for you and your domain.
Option 1. Set up DKIM for your emails
If you’re relying only on SPF for DMARC compliance, you’re likely to face this problem. One solution to this is to set up DKIM authentication for your emails. DKIM incorporates digitally verifiable signatures in the message body (and not the message header), hence discrepancies in the Mail From: address has no impact on DKIM authentication results. Since DMARC needs either SPF or DKIM alignment to pass, for it to deem an email as authentic (and not both), even if SPF fails due to domain misalignment when you send a calendar invite, if you’re email is signed with a DKIM signature, DMARC will pass for it.
Use our DKIM record generator tool to start creating your free record now. After our AI generates your record, please get in touch with your DNS hosting provider to publish this record on your DNS. You can also publish it yourself if you have access to your DNS management console.
Steps to create a DKIM record on Gmail
- Login to Google Workspace as the admin
- On your Google Admin Console settings for Gmail, click on “Authenticate Email“

- On the Authenticate Email page, enter your DKIM hostname and value created by clicking on the “Generate new record” button. Make sure you configure a selector of the desired bit size. The default selector for setting up DKIM on Google Workspace is “google” and it is recommended practice to keep this default value as your selector of choice.
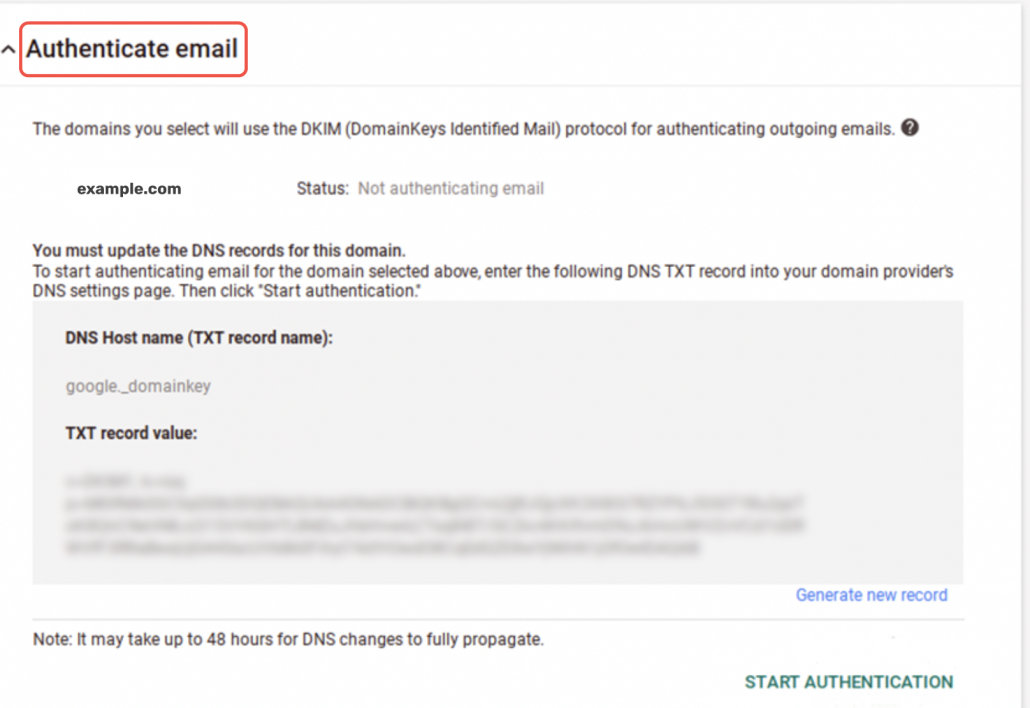
- Click on “START AUTHENTICATION”
Note: It may take up to 48 hours to process changes.
PowerDMARC practices DMARC compliance by incorporating both SPF and DKIM in your email authentication system for enhanced protection. We also help organizations successfully configure enforced policies without email losses or deliverability issues. If you’re facing issues implementing protocols, you can sign up for a free DMARC analyzer and let us handle everything for you.
Option 2. Change your DMARC policy mode to p=none
While we DO NOT RECOMMEND this method, using a relaxed mode like p=none will not affect your email deliverability or block out your Google Calendar invite responses. However, losing enforcement will expose your domain to spoofing and phishing attacks with no way to protect against domain impersonation, so exercise caution if you decide to choose this option.
Option 3. Use out-of-band response buttons
Let’s consider you have sent a google calendar invite from company.com (a google domain) to a mailbox hosted by a different mailbox provider (e.g aol.com). The recipient of this email can accept your invitation in 2 ways:
He can either use the out-of-band response button (which is added by his own mailbox provider), usually found at the top of the message:
Or, he can try to accept the invitation through the buttons attached by Google in the mail body when it sent the invitation to the recipient’s inbox:
If the recipient uses the former (out-of-band response buttons), all works fine as the response is sent through an aol.com server to your google domain, instructing whether to accept or reject the invitation.
However, if the recipient uses the latter, the email is rejected per DMARC reject policy. This is because this time the response is sent in the form of an email originating from a Google server to your Google domain, however, the Mail From: address displays the aol.com email address of the recipient. Beginning to see the problem here? This response is immediately blocked by Google in compliance with the invitation recipient’s DMARC reject policy.
If you’re the recipient, always try to use out-of-band response buttons while accepting calendar invites. If you’re the sender, you can inform your recipients about the same, to avoid this issue.
Option 4: Use outlook.com
If you use Microsoft’s email servers (such as outlook.com) for sending your email invite responses, your messages will not be blocked. This is because Microsoft is yet to upgrade its authentication policy to p=reject and allow spoofed emails to land in their recipients’ inboxes. While this isn’t ideal, it will help you bypass the DMARC reject filters and prevent your Google Calendar invites from being blocked.
Option 5: Include Google in your domain’s SPF record as an authorized sender
If you’re the invitee, you can make modifications to your domain’s SPF record to include google as an authorized sender. This will help you bypass rejection even if you use a google server to respond to your calendar invite while being hosted by a different mailbox provider.
Learn how to configure a Google SPF record from our knowledge base. If you already have an account at PowerDMARC and have enabled PowerSPF, our dynamic SPF flattening tool for your emails, you don’t have to worry about this issue. We handle source alignment for you, alerting you about IP address changes by your third parties. Sign up for your free SPF flattening tool now!
Hope this article helped you mitigate the problem with your google calendar invite responses blocked by DMARC. For expert assistance in configuring protocols, contact us today!
- Is Windows Defender Enough for Small Business Security? - May 14, 2026
- DMARCbis Explained – What’s Changing and How to Prepare - April 16, 2026
- SOA Serial Number Format Is Invalid: Causes & How to Fix It - April 13, 2026



