Key Takeaways
- A DNS server translates human-readable domain names into IP addresses, enabling user-friendly navigation on the internet.
- DNS servers work by receiving a domain name query from a client and forwarding it through a hierarchy of DNS servers until the corresponding IP address is found.
- There are various types of DNS servers, including recursive, authoritative, caching, and forwarding servers, each serving a specific function in the DNS resolution process.
- DNS servers not only simplify web access but also improve load distribution, redundancy, and security for website traffic.
- Understanding how DNS servers operate is crucial for troubleshooting internet connectivity issues and optimizing online performance.
Every time you type a website name and hit enter, something happens in the split-second before the page loads – a quiet lookup you never see, never think about, and rarely notice when it works. This is what a DNS server does.
In this article, we’ll cover how DNS servers work, the threats they face, and why they are a critical layer of internet security, especially when it comes to protecting email systems from spoofing and abuse.
What is a DNS Server?
A DNS server is what allows you to access websites using simple domain names instead of long numerical IP addresses. When you type a URL into your browser, a DNS server translates that name into the correct IP address so your request reaches the right destination.
It’s often described as the internet’s phonebook, but that comparison only explains part of the story. To be precise: DNS is the underlying system and protocol that makes domain resolution possible, while a DNS server is the infrastructure that runs it and responds to your queries.
Core Function
DNS servers translate human-friendly domain names into machine-readable IP addresses. For example: You type: wikipedia.org, your DNS returns: 208.80.154.224, your browser then connects to that IP address to load the page
This translation happens automatically in the background every time you visit a website, send an email, or use an app.
Why Not Just Use IP Addresses?
Technically, you could, but it would be impractical because:
- Remembering complex IP addresses like 142.250.190.46 is far harder than remembering google.com. Every site has a different IP, which makes it practically impossible to remember it all.
- Servers get migrated, swapped, or load-balanced across many machines. Domain names stay stable while the underlying IPs shift behind the scenes.
- Big sites use dozens or hundreds of IPs. DNS can route you to the closest or least-busy one without you knowing.
How DNS Resolution Works
Every time you visit a website or send an email, a DNS lookup happens in the background. While it feels instant, there is a structured process behind it.
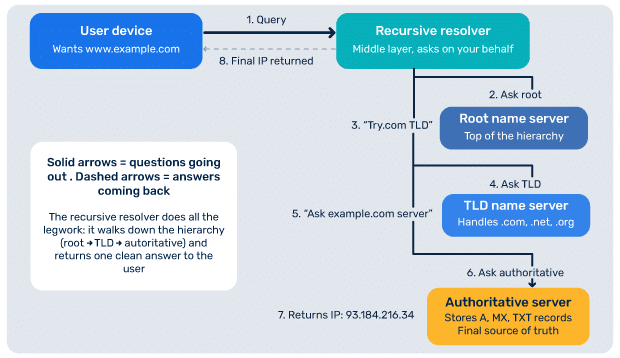
At a high level, the process looks like this:
- Your browser sends a query to a recursive resolver
- The resolver checks its cache for an existing answer
- If not found, it queries the root name servers
- The query is directed to the appropriate Top-Level Domain (TLD) server (.com, .org, etc.)
- The TLD server points to the authoritative name server
- The authoritative server returns the correct IP address
- The resolver caches the response based on Time to Live (TTL)
- Your browser connects to the destination server
Caching plays an important role here: If a DNS response is already stored, the process is much faster, but otherwise the full lookup chain is triggered. This system is efficient, but it also introduces points where things can go wrong or be manipulated.
You can check your domain’s DNS resolution in real time using our free DNS Lookup tool.
The 4 Core Types of DNS Servers
To understand DNS properly, it helps to know the roles different types of DNS servers play:
Recursive resolver
The recursive resolver is the first stop for your query. It acts as the middle layer between your device and the rest of the DNS system.
Root name servers
These servers sit at the top of the DNS hierarchy. They direct queries to the correct top-level domain servers.
TLD name servers
TLD name servers handle domain extensions like .com, .net, or .org and point queries toward the correct authoritative server.
Authoritative name servers
These provide the final answer. The authoritative name servers store the DNS records for a domain, including A records, MX records, and TXT records. For email and security, the authoritative server is especially important because this is where authentication records are stored.
DNS Security Threats: Why DNS Servers Are an Attack Surface
DNS was not originally designed with strong security in mind. As a result, it has become a frequent target for attackers. Some of the most common DNS attacks include:
DNS spoofing (cache poisoning)
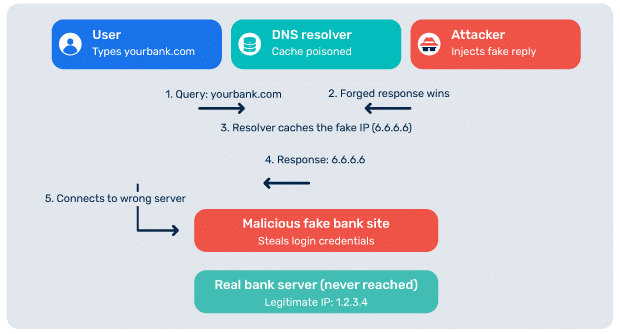
DNS spoofing is a security threat in which attackers inject false DNS information into a resolver’s cache. This can redirect users to malicious websites without their knowledge.
How it works:
When you type a URL like “yourbank.com” into your browser, your computer asks a DNS server to translate that name into an IP address (the server’s actual numerical address). DNS spoofing occurs when an attacker injects false information into the DNS lookup process. This causes the DNS server to return the IP address of a malicious server instead of the correct one. Your browser then connects to the attacker’s site, often without any obvious indication that something is wrong.
Risks of DNS spoofing:
- Attackers can build convincing fake versions of banking sites, email logins, or other services to steal credentials and personal data.
- They can also use it to distribute malware or to censor or surveil traffic. Because the URL in your browser still looks correct, victims often have no idea they’ve been redirected.
DNS hijacking
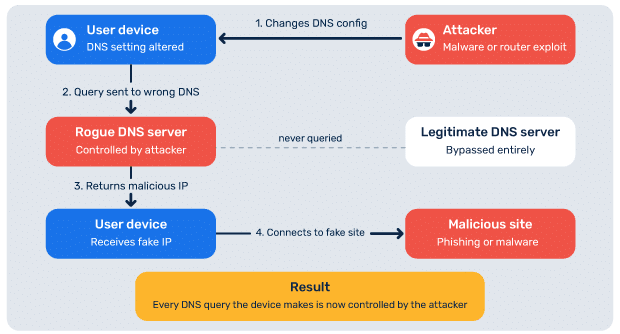
In DNS hijacking, attackers gain control of DNS settings or records. This allows them to reroute traffic, intercept communications, or manipulate services like email.
How it works:
There are several common ways DNS hijacking happens:
- In local hijacking, malware on your device changes your system’s DNS settings to point to a rogue server.
- In router hijacking, attackers exploit weak or default router credentials to alter the DNS settings on your home or office router, which then affects every device on the network.
- In man-in-the-middle hijacking, attackers intercept DNS traffic between you and your legitimate DNS server, modifying responses in transit.
- In rogue DNS server attacks, attackers compromise an actual DNS server at the Internet Service Provider (ISP) or organizational level, affecting potentially huge numbers of users at once.
Risks of DNS hijacking:
- Credential theft through fake login pages, malware distribution, ad injection, or surveillance.
- Redirecting users to advertising or search pages when they mistype a domain, or blocking access to certain sites.
DNS amplification attacks
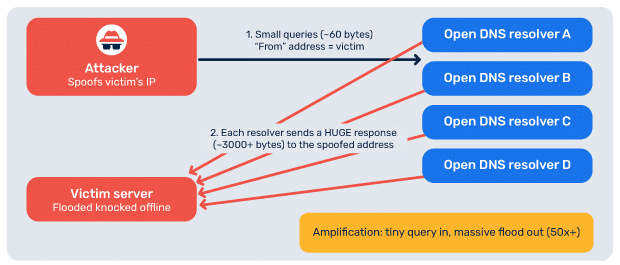
DNS amplification attacks are used in distributed denial-of-service attacks, where attackers overwhelm systems by exploiting DNS query responses.
How it works:
The attacker sends DNS queries to publicly accessible DNS resolvers, but spoofs the source IP address of those queries to make them appear to come from the victim’s IP. The DNS server, thinking the victim asked the question, sends its response to the victim instead of the attacker.
By choosing query types that produce large responses (like ANY queries or DNSSEC-related records), the attacker can turn a small request of around 60 bytes into a response of several thousand bytes. This amplification factor can be 50x or more, meaning an attacker with modest bandwidth can generate a flood many times larger directed at the victim.
Risks of DNS amplification attacks:
- Service downtime
- Loss of business revenue
- Potential reputational damage
How DNSSEC Helps Protect DNS Integrity
DNSSEC, or Domain Name System Security Extensions, adds a layer of verification to DNS responses. Instead of blindly trusting a DNS answer, DNSSEC ensures that the response is authentic and has not been altered in transit. It does this using cryptographic signatures. Here’s how it protects DNS integrity:
1. Prevents DNS spoofing: Attackers often try to inject fake DNS responses. With DNSSEC, the fake responses won’t have valid signatures, and therefore, your resolver discards them.
2. Ensures data hasn’t been modified: DNSSEC guarantees that the IP address you receive is exactly what the domain owner published, and no one altered it in transit.
3. Authenticates the source of data: DNSSEC confirms that the response really comes from the authoritative DNS server for that domain, and not from an attacker pretending to be one.
4. Creates a chain of trust: DNSSEC works through a hierarchy: Root zone → TLD (.com, .org) → domain, where each level validates the next using cryptographic keys. If any link fails, validation fails
You can check your DNSSEC configuration using our free DNSSEC checker tool.
In addition to DNSSEC, newer protocols like DNS over HTTPS (DoH) and DNS over TLS (DoT) help protect DNS queries from interception.
- DoH sends DNS queries over HTTPS (the same protocol used for secure web traffic), making them harder to distinguish from normal browsing and easier to bypass network filtering.
- DoT sends DNS queries over a dedicated encrypted TLS connection (typically port 853), offering strong privacy with clearer separation from regular web traffic.
While these technologies improve security, they are not always universally implemented. This leaves gaps that attackers can still exploit.
DNS and Email Authentication: The Direct Connection
DNS plays a central role in email authentication. Without DNS records (published on authoritative DNS servers), modern email security standards would not function.
Three key protocols rely entirely on DNS:
- Sender Policy Framework (SPF) records specify which servers are allowed to send email on behalf of a domain
- DomainKeys Identified Mail (DKIM) records publish public keys used to verify email signatures
- Domain-based Message Authentication Reporting & Conformance (DMARC) records define how receiving servers should handle failed authentication
All of these are stored as DNS records on the authoritative name server. This creates an important dependency. If your DNS is misconfigured or compromised, your email authentication can break down completely.
For example, if an attacker gains access to your DNS:
- They can modify SPF records to authorize malicious senders
- They can replace DKIM keys
- They can weaken or disable DMARC policies
Beyond these three core protocols, additional standards like Mail Transfer Agent Strict Transport Security (MTA-STS), Transport Layer Security Reporting (TLS-RPT), and Brand Indicators for Message Identification (BIMI) are also implemented through DNS records.
Troubleshooting: DNS Server Not Responding
One of the most common DNS-related issues users face is the “DNS server not responding” error. The error means your device successfully sent a DNS query, but didn’t get a reply back from the DNS server within the expected time. Without that reply, your browser can’t translate a domain name like google.com into an IP address, so the connection fails and you can’t reach the site, even though your internet connection itself might be working at a basic level.
This issue can happen due to:
- Network connectivity problems
- Misconfigured DNS settings
- Router or ISP issues
- Firewall or antivirus interference
- Temporary DNS server outages
In most cases, you can resolve it with a few basic steps:
Step 1: Restart your router and device
Unplug the power cable of your router and modem and wait for 30 seconds. Then plug the modem back in first, followed by the router cable, and wait another 1-2 mins before restarting your device.
Step 2: Flush your DNS cache
Your device keeps a local cache of DNS lookups to speed things up. If that cache contains stale or corrupted entries, your device might keep trying to contact a server that’s no longer reachable.
On Windows 10 or 11:
- Press the Windows key, type cmd, right-click “Command Prompt,” and select “Run as administrator.”
- In the black window that opens, type ipconfig /flushdns and press Enter.
- You should see a confirmation: “Successfully flushed the DNS Resolver Cache.”
On macOS:
- Open Terminal (press Cmd + Space, type “Terminal,” press Enter).
- Type sudo dscacheutil -flushcache; sudo killall -HUP mDNSResponder and press Enter.
- Enter your administrator password when prompted
Learn how to flush DNS in detail for different operating systems.
Step 3: Switch to a public DNS provider
Your ISP’s DNS servers are often slower, less reliable, and sometimes filtered or logged. Public DNS providers like Cloudflare and Google run massive global networks specifically optimized for fast, accurate DNS resolution.
Recommended servers are Cloudflare: 1.1.1.1 (primary) and 1.0.0.1 (secondary), or Google: 8.8.8.8 (primary) and 8.8.4.4 (secondary).
Step 4: Check your network adapter settings
Sometimes the adapter itself has bad settings, outdated drivers, or a corrupted protocol stack. Check your active connections, remove the connection, and reconnect back in to see if it helps resolve the issue.
Step 5: Disable conflicting security software temporarily
Antivirus suites, firewalls, and Virtual Private Networks (VPNs) often include their own DNS filtering or interception layers. When these misbehave, they can silently block legitimate DNS responses.
- Disconnect your VPN clients
- Pause protection for your third-party antivirus software
- Toggle off the firewall for your active network temporarily, test, and turn it back on immediately.
- Make sure no manual proxy is enabled unless you specifically need one.
Important note: If disabling one of these fixes the problem, the issue is in that software’s configuration, not the software itself. You shouldn’t leave security tools off; instead, reconfigure the offending tool (often by allowing your DNS server in its settings) or contact its support.
Final Thoughts: Why This Matters for Your Organization
A reliable DNS server is the foundation of a secure email program. For organizations that rely on email, choosing the right DNS server is even more critical.
A weak DNS server setup can lead to email spoofing and phishing attacks, loss of domain trust, delivery failures, and reputation damage. Laying a secure DNS foundation, combined with properly configured SPF, DKIM, and DMARC, is essential for protecting both your users and your brand.
Audit your domain’s DNS records with a free Domain Analyzer tool to confirm your email authentication protocols are correctly configured.
Frequently Asked Questions
What does a DNS server do?
A DNS server translates human-readable domain names into IP addresses so browsers can locate and load websites.
What is the difference between a DNS server and a DNS record?
A DNS server is the system that stores and responds to queries, while a DNS record is a specific entry (like an A or MX record) that defines how a domain should be resolved or handled.
What is the best DNS server to use?
The best DNS server depends on your needs, but popular, reliable options include Google Public DNS and Cloudflare for their speed, security, and global availability.