PowerDMARC’s Email Authentication Blog – Read the latest news and updates

Removable Media Security Threats
BlogsRemovable media threats can lead to large scale data leakage and loss, and impose heavy reputational damage.

The Ultimate Guide to Email Security: Types, Protocols, and Best Practices
BlogsEmail security is the process of protecting your email communications and information against cyberattacks and data breaches.
DMARC Tester – DMARC Testing Methods Explained
BlogsA DMARC Tester is an online DMARC testing tool that helps you test DMARC to uncover any abnormalities that may exist.
Zero-day Vulnerability: Definition and Examples?
BlogsZero-day vulnerability is a protocol, software, and application vulnerability not yet known to the general public or the product developers.
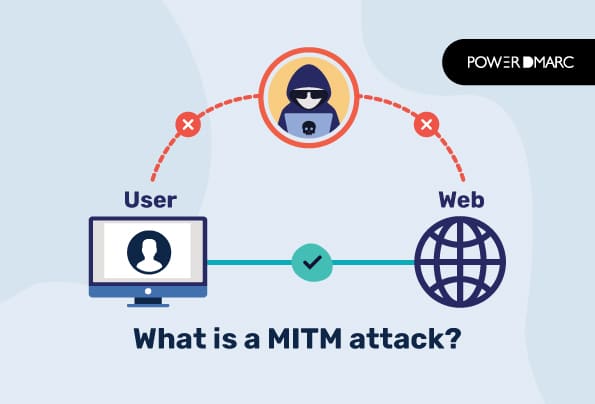
What is a MITM Attack?
Blogs In MITM attacks, hackers intercept communication and data transfer to steal sensitive details. This is done in two phases; encryption and decryption.
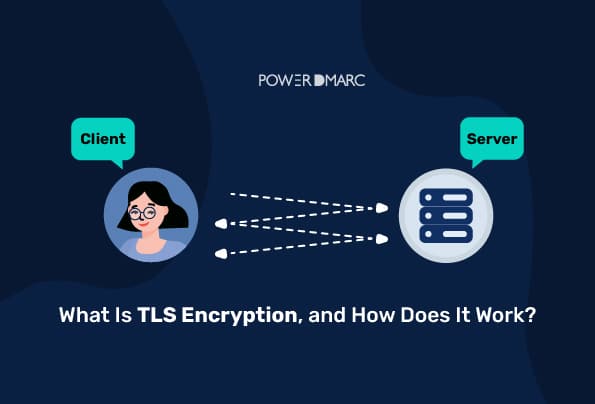
What Is TLS Encryption, and How Does It Work?
BlogsTLS (Transport Layer Security), is an Internet security protocol that provides authentication and encryption services between two communicating applications.

What is a Data Leak?
BlogsA data leak happens when sensitive or confidential information is exposed to unauthorized entities.

What is a Data Breach, and How to Prevent it?
BlogsA data breach is a cyberattack where private and sensitive information is disclosed to an unauthorized entity.
What is the Difference Between SSL and TLS?
BlogsWhile the two protocols encrypt data sent over the Internet, there is a marked diference between SSL and TLS.
Common Security Risks for Remote Workers
BlogsPhishing is an effective and dangerous cybercrime because it relies on people's inherent trust in the internet.
